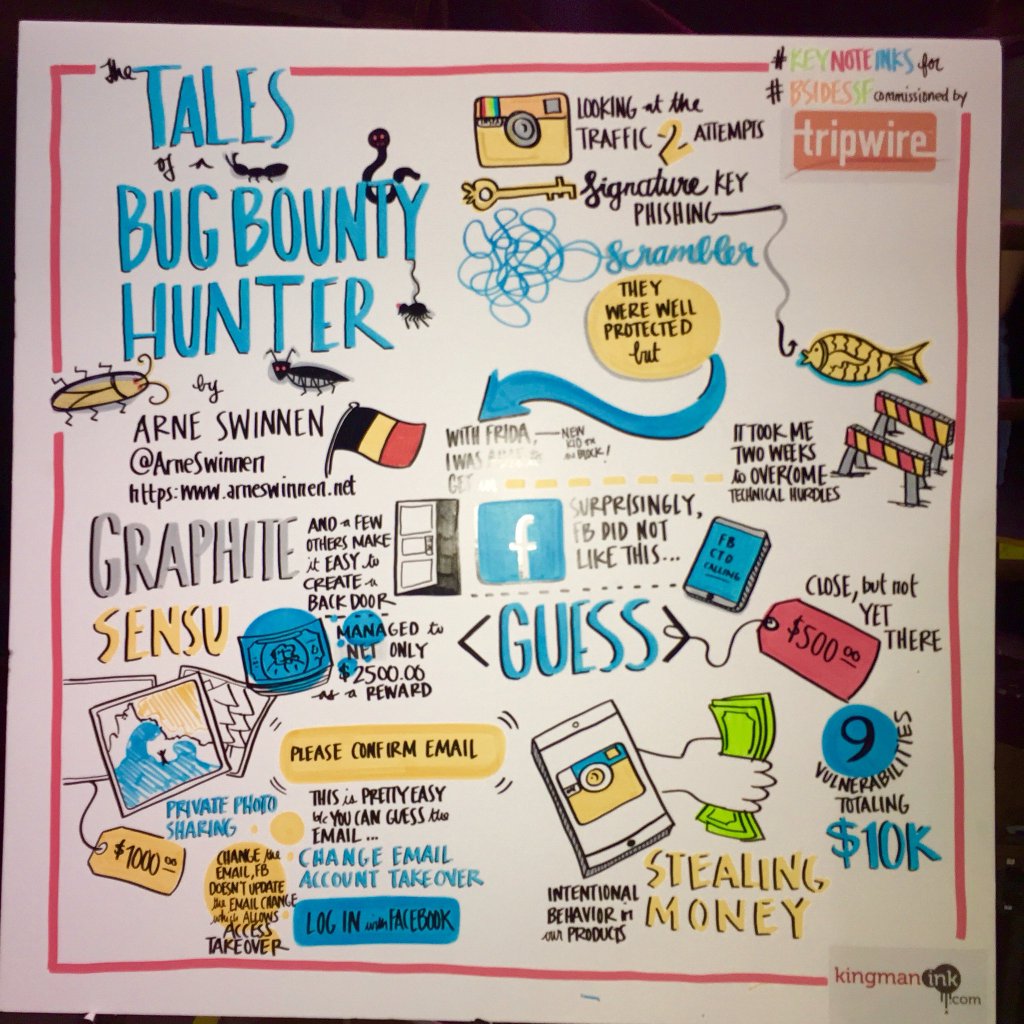
Abstract: Bug bounty hunting is the new black! During this technical talk, 10 interesting vulnerabilities identified in Instagram will be presented. All vulnerabilities were disclosed responsibly via Facebook’s Public Bug Bounty program over the course of 2015 and 2016, and will be discussed in depth. Required advanced Mobile Security attack techniques for this Research, such as Binary Modification, Dynamic Hooking and Burp Suite Plugin Development will be covered, among other trickery.
The most interesting vulnerabilities were hybrid: Combinations of complementary vulnerabilities in different environments (e.g. Web and Mobile). All identified issues’ root causes will be mapped onto the Software Development Life Cycle (SDLC), to analyze where they could have been prevented from materializing. Last but not least, the monetary rewards offered by Facebook for each vulnerability and general Bug Bounty Hunting advice will be shared with the community.
Conferences: BSidesSF16, SANS Night 2016, SecAppDev 2016, OWASP Benelux Day 2016
Slides: V1 (long), V2 (AppSecEU16)
Videos: BSidesSF (50min), AppSecEU16 (50min)