TL;DR: A rogue Android app could read any other App’s file metadata: filename, size, last modification date. If a filename contained sensitive predictable data, the rogue Android app could locally brute-force this, which was the case for Instagram on Android. Through the leakage of filesize and last modification date, a rogue Android app could monitor real-time usage of others apps. The file system permissions bug has been present in Android since the very beginning. Google rated this vulnerability as a low risk issue and paid out a $500 bug bounty.
Mobile Security
InstaBrute: Two Ways to Brute-force Instagram Account Credentials
TL;DR: Instagram contained two distinct vulnerabilities that allowed an attacker to brute-force passwords of user accounts. Combined with user enumeration, a weak password policy, no 2FA nor other mitigating security controls, this could have allowed an attacker to compromise many accounts without any user interaction, including high-profile ones. Facebook fixed both issues and awarded a combined bounty of $5.000. Continue Reading
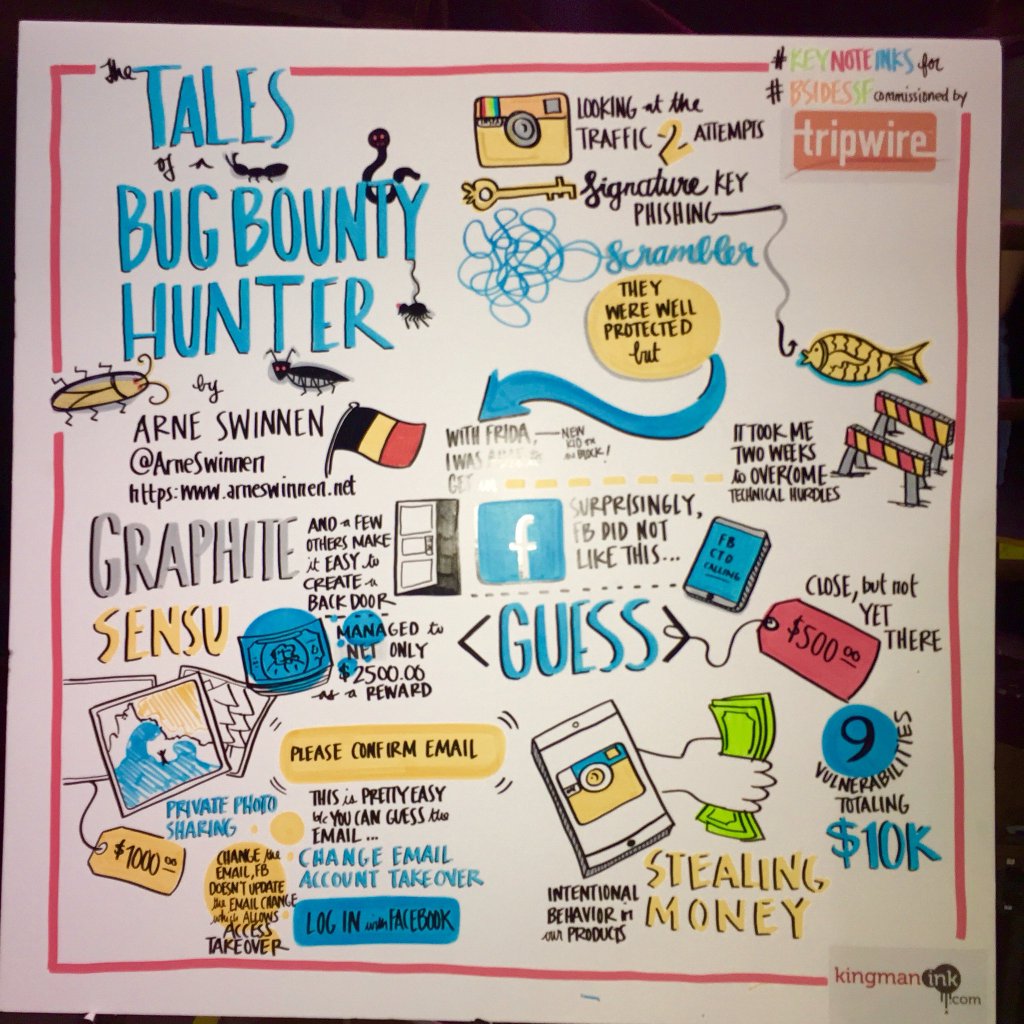
The Tales of a Bug Bounty Hunter: 10 Interesting Vulnerabilities in Instagram
Abstract: Bug bounty hunting is the new black! During this technical talk, 10 interesting vulnerabilities identified in Instagram will be presented. All vulnerabilities were disclosed responsibly via Facebook’s Public Bug Bounty program over the course of 2015 and 2016, and will be discussed in depth. Required advanced Mobile Security attack techniques for this Research, such as Binary Modification, Dynamic Hooking and Burp Suite Plugin Development will be covered, among other trickery.
The most interesting vulnerabilities were hybrid: Combinations of complementary vulnerabilities in different environments (e.g. Web and Mobile). All identified issues’ root causes will be mapped onto the Software Development Life Cycle (SDLC), to analyze where they could have been prevented from materializing. Last but not least, the monetary rewards offered by Facebook for each vulnerability and general Bug Bounty Hunting advice will be shared with the community.
Conferences: BSidesSF16, SANS Night 2016, SecAppDev 2016, OWASP Benelux Day 2016
Slides: V1 (long), V2 (AppSecEU16)
Videos: BSidesSF (50min), AppSecEU16 (50min)